| Section |
Page |
| ProSecure Unified Threat Management (UTM) Appliance |
1 |
| Contents |
5 |
| 1. Introduction |
15 |
| What Is the ProSecure Unified Threat Management (UTM) Appliance? |
15 |
| Key Features and Capabilities |
16 |
| Multiple WAN Port Models for Increased Reliability or Outbound Load Balancing |
17 |
| Wireless Features |
18 |
| DSL Features |
18 |
| Advanced VPN Support for Both IPSec and SSL |
18 |
| A Powerful, True Firewall |
19 |
| Stream Scanning for Content Filtering |
19 |
| Security Features |
20 |
| Autosensing Ethernet Connections with Auto Uplink |
20 |
| Extensive Protocol Support |
21 |
| Easy Installation and Management |
21 |
| Maintenance and Support |
22 |
| Model Comparison |
22 |
| Service Registration Card with License Keys |
23 |
| Package Contents |
24 |
| Hardware Features |
24 |
| Front Panel UTM5 and UTM10 |
25 |
| Front Panel UTM25 |
26 |
| Front Panel UTM50 |
26 |
| Front Panel UTM150 |
27 |
| Front Panel UTM9S and UTM25S and Network Modules |
28 |
| LED Descriptions, UTM5, UTM10, UTM25, UTM50, and UTM150 |
30 |
| LED Descriptions, UTM9S, UTM25S, and their Network Modules |
32 |
| Rear Panel UTM5, UTM10, and UTM25 |
33 |
| Rear Panel UTM50 and UTM150 |
34 |
| Rear Panel UTM9S and UTM25S |
35 |
| Bottom Panels with Product Labels |
36 |
| Choose a Location for the UTM |
39 |
| Use the Rack-Mounting Kit |
40 |
| 2. Use the Setup Wizard to Provision the UTM in Your Network |
41 |
| Steps for Initial Connection |
41 |
| Qualified Web Browsers |
42 |
| Requirements for Entering IP Addresses |
42 |
| Log In to the UTM |
42 |
| Web Management Interface Menu Layout |
44 |
| Use the Setup Wizard to Perform the Initial Configuration |
47 |
| Setup Wizard Step 1 of 10: LAN Settings |
48 |
| Setup Wizard Step 2 of 10: WAN Settings |
51 |
| Setup Wizard Step 3 of 10: System Date and Time |
54 |
| Setup Wizard Step 4 of 10: Services |
55 |
| Setup Wizard Step 5 of 10: Email Security |
57 |
| Setup Wizard Step 6 of 10: Web Security |
58 |
| Setup Wizard Step 7 of 10: Web Categories to Be Blocked |
60 |
| Setup Wizard Step 8 of 10: Email Notification |
62 |
| Setup Wizard Step 9 of 10: Signatures & Engine |
63 |
| Setup Wizard Step 10 of 10: Saving the Configuration |
64 |
| Register the UTM with NETGEAR |
65 |
| Use the Web Management Interface to Activate Licenses |
65 |
| Electronic Licensing |
67 |
| Automatic Retrieval of Licenses after a Factory Default Reset |
67 |
| Verify Correct Installation |
68 |
| Test Connectivity |
68 |
| Test HTTP Scanning |
68 |
| What to Do Next |
68 |
| 3. Manually Configure Internet and WAN Settings |
70 |
| Internet and WAN Configuration Tasks |
71 |
| Automatically Detecting and Connecting the Internet Connections |
71 |
| Manually Configure the Internet Connection |
75 |
| Configure the WAN Mode |
80 |
| Overview of the WAN Modes |
80 |
| Configure Network Address Translation (All Models) |
81 |
| Configure Classical Routing (All Models) |
82 |
| Configure Auto-Rollover Mode and the Failure Detection Method (Multiple WAN Port Models) |
82 |
| Configure Load Balancing and Optional Protocol Binding (Multiple WAN Port Models) |
85 |
| Configure Secondary WAN Addresses |
89 |
| Configure Dynamic DNS |
91 |
| Set the UTM’s MAC Address and Configure Advanced WAN Options |
94 |
| Additional WAN-Related Configuration Tasks |
97 |
| 4. LAN Configuration |
98 |
| Manage Virtual LANs and DHCP Options |
98 |
| Port-Based VLANs |
99 |
| Assign and Manage VLAN Profiles |
100 |
| VLAN DHCP Options |
101 |
| Configure a VLAN Profile |
103 |
| Configure VLAN MAC Addresses and Advanced LAN Settings |
108 |
| Configure Multihome LAN IP Addresses on the Default VLAN |
109 |
| Manage Groups and Hosts (LAN Groups) |
111 |
| Manage the Network Database |
112 |
| Change Group Names in the Network Database |
115 |
| Set Up Address Reservation |
116 |
| Configure and Enable the DMZ Port |
117 |
| Manage Routing |
121 |
| Configure Static Routes |
121 |
| Configure Routing Information Protocol |
123 |
| Static Route Example |
126 |
| 5. Firewall Protection |
127 |
| About Firewall Protection |
127 |
| Administrator Tips |
128 |
| Overview of Rules to Block or Allow Specific Kinds of Traffic |
128 |
| Outbound Rules (Service Blocking) |
129 |
| Inbound Rules (Port Forwarding) |
133 |
| Order of Precedence for Rules |
138 |
| Configure LAN WAN Rules |
139 |
| Create LAN WAN Outbound Service Rules |
140 |
| Create LAN WAN Inbound Service Rules |
141 |
| Configure DMZ WAN Rules |
142 |
| Create DMZ WAN Outbound Service Rules |
144 |
| Create DMZ WAN Inbound Service Rules |
144 |
| Configure LAN DMZ Rules |
145 |
| Create LAN DMZ Outbound Service Rules |
147 |
| Create LAN DMZ Inbound Service Rules |
147 |
| Examples of Firewall Rules |
148 |
| Inbound Rule Examples |
148 |
| Outbound Rule Example |
153 |
| Configure Other Firewall Features |
154 |
| VLAN Rules |
154 |
| Attack Checks, VPN Pass-through, and Multicast Pass-through |
157 |
| Set Session Limits |
160 |
| Manage the Application Level Gateway for SIP Sessions and VPN Scanning |
161 |
| Create Services, QoS Profiles, Bandwidth Profiles, and Traffic Meter Profiles |
162 |
| Add Customized Services |
163 |
| Create Service Groups |
165 |
| Create IP Groups |
167 |
| Create Quality of Service Profiles |
169 |
| Create Bandwidth Profiles |
171 |
| Create Traffic Meter Profiles |
174 |
| Set a Schedule to Block or Allow Specific Traffic |
177 |
| Enable Source MAC Filtering |
179 |
| Set Up IP/MAC Bindings |
181 |
| Configure Port Triggering |
183 |
| Configure Universal Plug and Play |
186 |
| Enable and Configure the Intrusion Prevention System |
187 |
| 6. Content Filtering and Optimizing Scans |
192 |
| About Content Filtering and Scans |
192 |
| Default Email and Web Scan Settings |
193 |
| Configure Email Protection |
194 |
| Customize Email Protocol Scan Settings |
194 |
| Customize Email Antivirus and Notification Settings |
196 |
| Email Content Filtering |
199 |
| Protect Against Email Spam |
202 |
| Configure Web and Services Protection |
210 |
| Customize Web Protocol Scan Settings |
210 |
| Configure HTTPS Smart Block |
212 |
| Configure Web Malware or Antivirus Scans |
216 |
| Configure Web Content Filtering |
218 |
| Configure Web URL Filtering |
224 |
| Configure HTTPS Scanning and SSL Certificates |
228 |
| How HTTPS Scanning Works |
228 |
| Configure the HTTPS Scan Settings |
230 |
| Manage SSL Certificates for HTTPS Scanning |
231 |
| Specify Trusted Hosts for HTTPS Scanning |
235 |
| Configure the SSL Settings for HTTPS Scanning |
237 |
| Configure FTP Scanning |
238 |
| Customize FTP Antivirus Settings |
238 |
| Configure FTP Content Filtering |
239 |
| Configure Application Control |
240 |
| Set Exception Rules for Web and Application Access |
248 |
| Create Custom Categories for Exceptions for Web and Application Access |
258 |
| Set Scanning Exclusions for IP Addresses and Ports |
262 |
| 7. Virtual Private Networking Using IPSec, PPTP, or L2TP Connections |
264 |
| Considerations for Dual WAN Port Systems (Multiple WAN Port Models Only) |
264 |
| Use the IPSec VPN Wizard for Client and Gateway Configurations |
266 |
| Create Gateway-to-Gateway VPN Tunnels with the Wizard |
266 |
| Create a Client-to-Gateway VPN Tunnel |
271 |
| Test the Connection and View Connection and Status Information |
287 |
| Test the NETGEAR VPN Client Connection |
287 |
| NETGEAR VPN Client Status and Log Information |
289 |
| View the UTM IPSec VPN Connection Status |
289 |
| View the UTM IPSec VPN Log |
290 |
| Manage IPSec VPN and IKE Policies |
291 |
| Manage IKE Policies |
292 |
| Manage VPN Policies |
300 |
| Configure Extended Authentication (XAUTH) |
308 |
| Configure XAUTH for VPN Clients |
309 |
| User Database Configuration |
310 |
| RADIUS Client and Server Configuration |
310 |
| Assign IP Addresses to Remote Users (Mode Config) |
312 |
| Mode Config Operation |
312 |
| Configure Mode Config Operation on the UTM |
312 |
| Configure the ProSafe VPN Client for Mode Config Operation |
319 |
| Test the Mode Config Connection |
326 |
| Modify or Delete a Mode Config Record |
327 |
| Configure Keep-Alives and Dead Peer Detection |
328 |
| Configure Keep-Alives |
328 |
| Configure Dead Peer Detection |
329 |
| Configure NetBIOS Bridging with IPSec VPN |
330 |
| Configure the PPTP Server |
331 |
| View the Active PPTP Users |
333 |
| Configure the L2TP Server |
334 |
| View the Active L2TP Users |
336 |
| For More IPSec VPN Information |
336 |
| 8. Virtual Private Networking Using SSL Connections |
337 |
| SSL VPN Portal Options |
337 |
| Build a Portal Using the SSL VPN Wizard |
338 |
| SSL VPN Wizard Step 1 of 6 (Portal Settings) |
339 |
| SSL VPN Wizard Step 2 of 6 (Domain Settings) |
342 |
| SSL VPN Wizard Step 3 of 6 (User Settings) |
347 |
| SSL VPN Wizard Step 4 of 6 (Client IP Addresses and Routes) |
348 |
| SSL VPN Wizard Step 5 of 6 (Port Forwarding) |
350 |
| SSL VPN Wizard Step 6 of 6 (Verify and Save Your Settings) |
351 |
| Access the New SSL VPN Portal |
353 |
| View the UTM SSL VPN Connection Status |
356 |
| View the UTM SSL VPN Log |
357 |
| Manually Configure and Modify SSL Portals |
357 |
| Manually Create or Modify the Portal Layout |
359 |
| Configure Domains, Groups, and Users |
362 |
| Configure Applications for Port Forwarding |
363 |
| Configure the SSL VPN Client |
365 |
| Use Network Resource Objects to Simplify Policies |
369 |
| Configure User, Group, and Global Policies |
371 |
| For More SSL VPN Information |
377 |
| 9. Manage Users, Authentication, and VPN Certificates |
378 |
| Authentication Process and Options |
378 |
| Configure Authentication Domains, Groups, and Users |
380 |
| Login Portals |
380 |
| Active Directories and LDAP Configurations |
384 |
| Configure Domains |
388 |
| Configure Groups |
394 |
| Configure Custom Groups |
397 |
| Configure User Accounts |
401 |
| Set User Login Policies |
404 |
| Change Passwords and Other User Settings |
408 |
| DC Agent |
409 |
| Configure RADIUS VLANs |
415 |
| Configure Global User Settings |
416 |
| View and Log Out Active Users |
417 |
| Manage Digital Certificates for VPN Connections |
419 |
| VPN Certificates Screen |
420 |
| Manage CA Certificates |
421 |
| Manage Self-Signed Certificates |
422 |
| Manage the Certificate Revocation List |
426 |
| 10. Network and System Management |
428 |
| Performance Management |
428 |
| Bandwidth Capacity |
428 |
| Features That Reduce Traffic |
429 |
| Features That Increase Traffic |
432 |
| Use QoS and Bandwidth Assignments to Shift the Traffic Mix |
435 |
| Monitoring Tools for Traffic Management |
436 |
| System Management |
436 |
| Change Passwords and Administrator and Guest Settings |
436 |
| Configure Remote Management Access |
438 |
| Use a Simple Network Management Protocol Manager |
440 |
| Manage the Configuration File |
445 |
| Update the Firmware |
448 |
| Update the Scan Signatures and Scan Engine Firmware |
454 |
| Configure Date and Time Service |
456 |
| Connect to a ReadyNAS and Configure Quarantine Settings |
458 |
| Log Storage |
459 |
| Connect to a ReadyNAS |
459 |
| Configure the Quarantine Settings |
460 |
| 11. Monitor System Access and Performance |
462 |
| Enable the WAN Traffic Meter |
462 |
| Configure Logging, Alerts, and Event Notifications |
466 |
| Configure the Email Notification Server |
466 |
| Configure and Activate System, Email, and Syslog Logs |
467 |
| How to Send Syslogs over a VPN Tunnel between Sites |
471 |
| Configure and Activate Update Failure and Attack Alerts |
473 |
| Configure and Activate Firewall Logs |
476 |
| Monitor Real-Time Traffic, Security, and Statistics |
477 |
| Monitor Application Use in Real Time |
483 |
| View Status Screens |
486 |
| View the System Status |
486 |
| View the Active VPN Users |
499 |
| View the VPN Tunnel Connection Status |
500 |
| View the Active PPTP and L2TP Users |
501 |
| View the Port Triggering Status |
502 |
| View the WAN, xDSL, or USB Port Status |
504 |
| View Attached Devices and the DHCP Leases |
505 |
| Query and Manage the Logs |
507 |
| Overview of the Logs |
508 |
| Query and Download Logs |
509 |
| Example: Use the Logs to Identify Infected Clients |
513 |
| Log Management |
514 |
| Query and Manage the Quarantine Logs |
514 |
| Query the Quarantined Logs |
515 |
| View and Manage the Quarantined Spam Table |
517 |
| View and Manage the Quarantined Infected Files Table |
518 |
| Spam Reports for End Users |
519 |
| View, Schedule, and Generate Reports |
520 |
| Enable Application Session Monitoring |
521 |
| Report Filtering Options |
522 |
| Use Report Templates and View Reports Onscreen |
524 |
| Schedule, Email, and Manage Reports |
529 |
| Use Diagnostics Utilities |
531 |
| Use the Network Diagnostic Tools |
532 |
| Use the Real-Time Traffic Diagnostics Tool |
533 |
| Gather Important Log Information and Generate a Network Statistics Report |
534 |
| Perform Maintenance on the USB Device, Reboot the UTM, or Shut Down the UTM |
536 |
| 12. Troubleshoot and Use Online Support |
538 |
| Basic Functioning |
539 |
| Verify the Correct Sequence of Events at Startup |
539 |
| Power LED Not On |
539 |
| Test LED Never Turns Off |
539 |
| LAN or WAN Port LEDs Not On |
540 |
| Troubleshoot the Web Management Interface |
540 |
| When You Enter a URL or IP Address, a Time-Out Error Occurs |
541 |
| Troubleshoot the ISP Connection |
541 |
| Troubleshoot a TCP/IP Network Using a Ping Utility |
543 |
| Test the LAN Path to Your UTM |
543 |
| Test the Path from Your Computer to a Remote Device |
544 |
| Restore the Default Configuration and Password |
545 |
| Problems with Date and Time |
546 |
| Use Online Support |
546 |
| Enable Remote Troubleshooting |
546 |
| Send Suspicious Files to NETGEAR for Analysis |
547 |
| Access the Knowledge Base and Documentation |
548 |
| A. xDSL Network Module for the UTM9S and UTM25S |
549 |
| xDSL Network Module Configuration Tasks |
550 |
| Configure the xDSL Settings |
550 |
| Automatically Detecting and Connecting the xDSL Internet Connection |
553 |
| Manually Configure the xDSL Internet Connection |
556 |
| Configure the WAN Mode |
561 |
| Overview of the WAN Modes |
561 |
| Configure Network Address Translation |
562 |
| Configure Classical Routing |
563 |
| Configure Auto-Rollover Mode and the Failure Detection Method |
563 |
| Configure Load Balancing and Optional Protocol Binding |
566 |
| Configure Secondary WAN Addresses |
570 |
| Configure Dynamic DNS |
572 |
| Set the UTM’s MAC Address and Configure Advanced WAN Options |
574 |
| Additional WAN-Related Configuration Tasks |
577 |
| B. Wireless Network Module for the UTM9S and UTM25S |
578 |
| Overview of the Wireless Network Module |
579 |
| Configuration Order |
579 |
| Wireless Equipment Placement and Range Guidelines |
579 |
| Configure the Basic Radio Settings |
580 |
| Operating Frequency (Channel) Guidelines |
583 |
| Wireless Data Security Options |
584 |
| Wireless Security Profiles |
585 |
| Before You Change the SSID, WEP, and WPA Settings |
587 |
| Configure and Enable Wireless Profiles |
588 |
| Restrict Wireless Access by MAC Address |
593 |
| View the Access Point Status and Connected Clients for a Wireless Profile |
595 |
| Configure a Wireless Distribution System |
596 |
| Configure Advanced Radio Settings |
598 |
| Configure WMM QoS Priority Settings |
600 |
| Test Basic Wireless Connectivity |
602 |
| For More Information About Wireless Configurations |
602 |
| C. 3G/4G Dongles for the UTM9S and UTM25S |
603 |
| 3G/4G Dongle Configuration Tasks |
603 |
| Manually Configure the USB Internet Connection |
604 |
| Configure the 3G/4G Settings |
608 |
| Configure the WAN Mode |
610 |
| Overview of the WAN Modes |
611 |
| Configure Network Address Translation |
612 |
| Configure Classical Routing |
613 |
| Configure Load Balancing and Optional Protocol Binding |
614 |
| Configure Dynamic DNS |
618 |
| Additional WAN-Related Configuration Tasks |
621 |
| D. Network Planning for Dual WAN Ports (Multiple WAN Port Models Only) |
622 |
| What to Consider Before You Begin |
622 |
| Plan Your Network and Network Management and Set Up Accounts |
622 |
| Cabling and Computer Hardware Requirements |
624 |
| Computer Network Configuration Requirements |
624 |
| Internet Configuration Requirements |
624 |
| Overview of the Planning Process |
626 |
| Inbound Traffic |
627 |
| Inbound Traffic to a Single WAN Port System |
628 |
| Inbound Traffic to a Dual WAN Port System |
628 |
| Virtual Private Networks |
629 |
| VPN Road Warrior (Client-to-Gateway) |
630 |
| VPN Gateway-to-Gateway |
633 |
| VPN Telecommuter (Client-to-Gateway through a NAT Router) |
635 |
| E. ReadyNAS Integration |
638 |
| Supported ReadyNAS Models |
638 |
| Install the UTM Add-On on the ReadyNAS |
639 |
| Connect to the ReadyNAS on the UTM |
641 |
| F. Two-Factor Authentication |
644 |
| Why Do I Need Two-Factor Authentication? |
644 |
| What Are the Benefits of Two-Factor Authentication? |
644 |
| What Is Two-Factor Authentication? |
645 |
| NETGEAR Two-Factor Authentication Solutions |
645 |
| G. System Logs and Error Messages |
648 |
| System Log Messages |
649 |
| System Startup |
649 |
| Reboot |
649 |
| NTP |
650 |
| Login/Logout |
650 |
| Firewall Restart |
651 |
| IPSec Restart |
651 |
| WAN Status |
651 |
| Traffic Metering Logs |
655 |
| Unicast, Multicast, and Broadcast Logs |
655 |
| Invalid Packet Logging |
656 |
| Service Logs |
658 |
| Content-Filtering and Security Logs |
658 |
| Web Filtering and Content-Filtering Logs |
659 |
| Spam Logs |
660 |
| Traffic Logs |
661 |
| Malware Logs |
661 |
| Email Filter Logs |
661 |
| IPS Logs |
662 |
| Anomaly Behavior Logs |
662 |
| Application Logs |
663 |
| Routing Logs |
663 |
| LAN-to-WAN Logs |
663 |
| LAN-to-DMZ Logs |
664 |
| DMZ-to-WAN Logs |
664 |
| WAN-to-LAN Logs |
664 |
| DMZ-to-LAN Logs |
665 |
| WAN-to-DMZ Logs |
665 |
| H. Default Settings and Technical Specifications |
666 |
| Default Settings |
666 |
| Physical and Technical Specifications |
673 |
| I. Notification of Compliance (Wired) |
677 |
| J. Notification of Compliance (Wireless) |
681 |

 1
1 2
2 3
3 4
4 5
5 6
6 7
7 8
8 9
9 10
10 11
11 12
12 13
13 14
14 15
15 16
16 17
17 18
18 19
19 20
20 21
21 22
22 23
23 24
24 25
25 26
26 27
27 28
28 29
29 30
30 31
31 32
32 33
33 34
34 35
35 36
36 37
37 38
38 39
39 40
40 41
41 42
42 43
43 44
44 45
45 46
46 47
47 48
48 49
49 50
50 51
51 52
52 53
53 54
54 55
55 56
56 57
57 58
58 59
59 60
60 61
61 62
62 63
63 64
64 65
65 66
66 67
67 68
68 69
69 70
70 71
71 72
72 73
73 74
74 75
75 76
76 77
77 78
78 79
79 80
80 81
81 82
82 83
83 84
84 85
85 86
86 87
87 88
88 89
89 90
90 91
91 92
92 93
93 94
94 95
95 96
96 97
97 98
98 99
99 100
100 101
101 102
102 103
103 104
104 105
105 106
106 107
107 108
108 109
109 110
110 111
111 112
112 113
113 114
114 115
115 116
116 117
117 118
118 119
119 120
120 121
121 122
122 123
123 124
124 125
125 126
126 127
127 128
128 129
129 130
130 131
131 132
132 133
133 134
134 135
135 136
136 137
137 138
138 139
139 140
140 141
141 142
142 143
143 144
144 145
145 146
146 147
147 148
148 149
149 150
150 151
151 152
152 153
153 154
154 155
155 156
156 157
157 158
158 159
159 160
160 161
161 162
162 163
163 164
164 165
165 166
166 167
167 168
168 169
169 170
170 171
171 172
172 173
173 174
174 175
175 176
176 177
177 178
178 179
179 180
180 181
181 182
182 183
183 184
184 185
185 186
186 187
187 188
188 189
189 190
190 191
191 192
192 193
193 194
194 195
195 196
196 197
197 198
198 199
199 200
200 201
201 202
202 203
203 204
204 205
205 206
206 207
207 208
208 209
209 210
210 211
211 212
212 213
213 214
214 215
215 216
216 217
217 218
218 219
219 220
220 221
221 222
222 223
223 224
224 225
225 226
226 227
227 228
228 229
229 230
230 231
231 232
232 233
233 234
234 235
235 236
236 237
237 238
238 239
239 240
240 241
241 242
242 243
243 244
244 245
245 246
246 247
247 248
248 249
249 250
250 251
251 252
252 253
253 254
254 255
255 256
256 257
257 258
258 259
259 260
260 261
261 262
262 263
263 264
264 265
265 266
266 267
267 268
268 269
269 270
270 271
271 272
272 273
273 274
274 275
275 276
276 277
277 278
278 279
279 280
280 281
281 282
282 283
283 284
284 285
285 286
286 287
287 288
288 289
289 290
290 291
291 292
292 293
293 294
294 295
295 296
296 297
297 298
298 299
299 300
300 301
301 302
302 303
303 304
304 305
305 306
306 307
307 308
308 309
309 310
310 311
311 312
312 313
313 314
314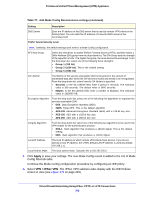 315
315 316
316 317
317 318
318 319
319 320
320 321
321 322
322 323
323 324
324 325
325 326
326 327
327 328
328 329
329 330
330 331
331 332
332 333
333 334
334 335
335 336
336 337
337 338
338 339
339 340
340 341
341 342
342 343
343 344
344 345
345 346
346 347
347 348
348 349
349 350
350 351
351 352
352 353
353 354
354 355
355 356
356 357
357 358
358 359
359 360
360 361
361 362
362 363
363 364
364 365
365 366
366 367
367 368
368 369
369 370
370 371
371 372
372 373
373 374
374 375
375 376
376 377
377 378
378 379
379 380
380 381
381 382
382 383
383 384
384 385
385 386
386 387
387 388
388 389
389 390
390 391
391 392
392 393
393 394
394 395
395 396
396 397
397 398
398 399
399 400
400 401
401 402
402 403
403 404
404 405
405 406
406 407
407 408
408 409
409 410
410 411
411 412
412 413
413 414
414 415
415 416
416 417
417 418
418 419
419 420
420 421
421 422
422 423
423 424
424 425
425 426
426 427
427 428
428 429
429 430
430 431
431 432
432 433
433 434
434 435
435 436
436 437
437 438
438 439
439 440
440 441
441 442
442 443
443 444
444 445
445 446
446 447
447 448
448 449
449 450
450 451
451 452
452 453
453 454
454 455
455 456
456 457
457 458
458 459
459 460
460 461
461 462
462 463
463 464
464 465
465 466
466 467
467 468
468 469
469 470
470 471
471 472
472 473
473 474
474 475
475 476
476 477
477 478
478 479
479 480
480 481
481 482
482 483
483 484
484 485
485 486
486 487
487 488
488 489
489 490
490 491
491 492
492 493
493 494
494 495
495 496
496 497
497 498
498 499
499 500
500 501
501 502
502 503
503 504
504 505
505 506
506 507
507 508
508 509
509 510
510 511
511 512
512 513
513 514
514 515
515 516
516 517
517 518
518 519
519 520
520 521
521 522
522 523
523 524
524 525
525 526
526 527
527 528
528 529
529 530
530 531
531 532
532 533
533 534
534 535
535 536
536 537
537 538
538 539
539 540
540 541
541 542
542 543
543 544
544 545
545 546
546 547
547 548
548 549
549 550
550 551
551 552
552 553
553 554
554 555
555 556
556 557
557 558
558 559
559 560
560 561
561 562
562 563
563 564
564 565
565 566
566 567
567 568
568 569
569 570
570 571
571 572
572 573
573 574
574 575
575 576
576 577
577 578
578 579
579 580
580 581
581 582
582 583
583 584
584 585
585 586
586 587
587 588
588 589
589 590
590 591
591 592
592 593
593 594
594 595
595 596
596 597
597 598
598 599
599 600
600 601
601 602
602 603
603 604
604 605
605 606
606 607
607 608
608 609
609 610
610 611
611 612
612 613
613 614
614 615
615 616
616 617
617 618
618 619
619 620
620 621
621 622
622 623
623 624
624 625
625 626
626 627
627 628
628 629
629 630
630 631
631 632
632 633
633 634
634 635
635 636
636 637
637 638
638 639
639 640
640 641
641 642
642 643
643 644
644 645
645 646
646 647
647 648
648 649
649 650
650 651
651 652
652 653
653 654
654 655
655 656
656 657
657 658
658 659
659 660
660 661
661 662
662 663
663 664
664 665
665 666
666 667
667 668
668 669
669 670
670 671
671 672
672 673
673 674
674 675
675 676
676 677
677 678
678 679
679 680
680 681
681 682
682 683
683 684
684 685
685 686
686 687
687 688
688 689
689 690
690 691
691 692
692 693
693 694
694 695
695 696
696 697
697 698
698 699
699 700
700 701
701 702
702 703
703 704
704


